Top 10 Cloud Security Providers for Small Businesses in 2026
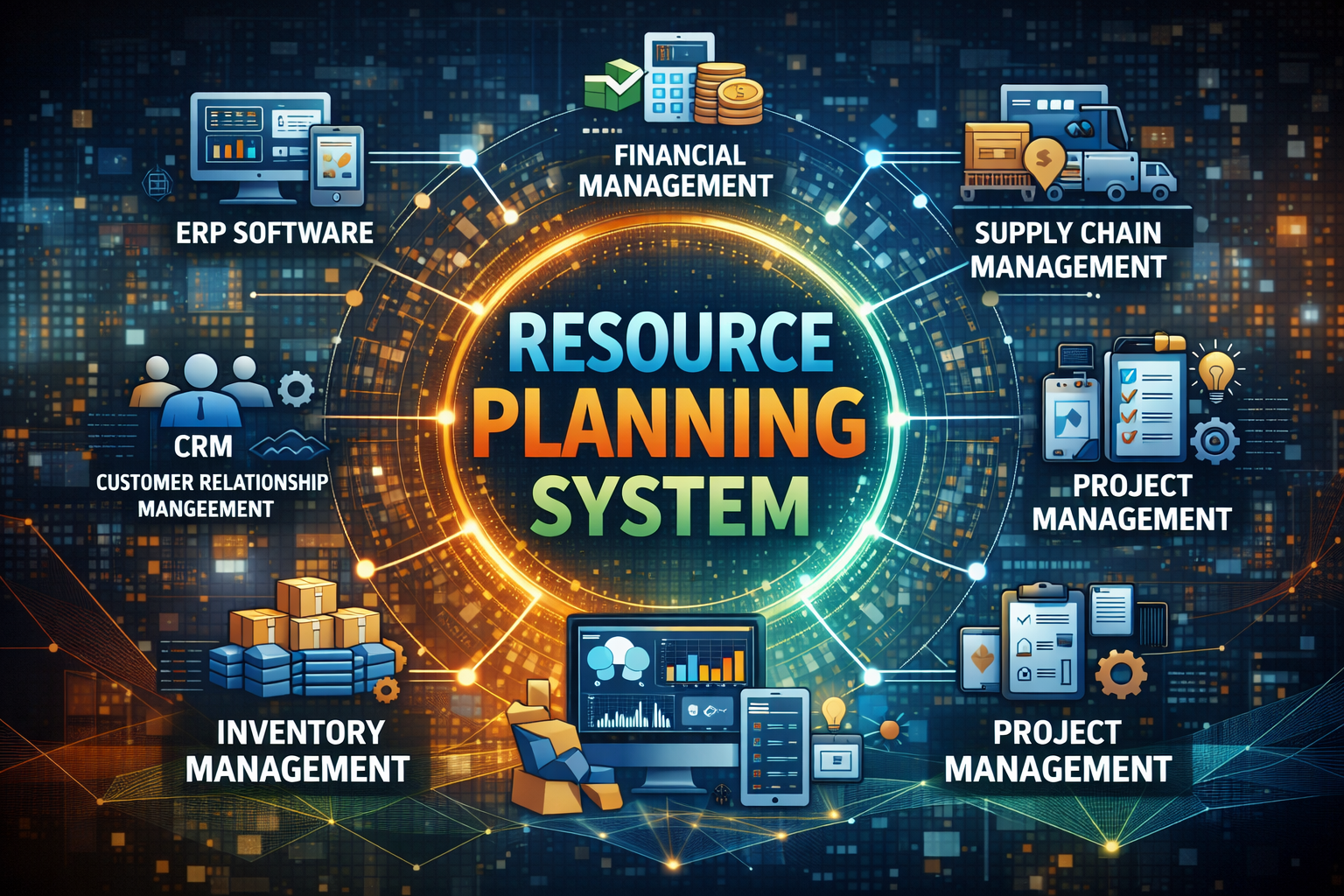
Cloud adoption among small businesses has accelerated rapidly over the last few years. From accounting software and customer relationship management (CRM) tools to data storage and remote collaboration platforms, the cloud is now central to daily operations. However, as reliance on cloud services increases, so do cybersecurity risks. Data breaches, ransomware attacks, misconfigurations, and compliance